CyberProof’s Cyber Threat Intelligence (CTI) team discovered a new cyber crime marketplace using advanced threat intelligence techniques. The marketplace – named, Plugged – deals with multiple carding methods and seems to be focused mainly on goods connected to companies in the UK.
What is Plugged?
The Plugged marketplace was developed in September 2019 by a threat actor named Nerds, an expert in carding scams and in cyber crime in general. The website claims that the marketplace has more than 15,000 customers.
Five agents provide the site’s customers with support. These agents may be Plugged vendors or other threat actors who have business relationships with Nerds.
The website provides detailed information about marketplace operations, product delivery, and payment methods most likely to increase trust and receive positive feedback, which in turn will help increase the market share.
Nerds claims Plugged is the best marketplace in the underground community, storing 90 percent of the information that’s shared on ICQ, Telegram and other platforms – i.e., goods offered for sale.
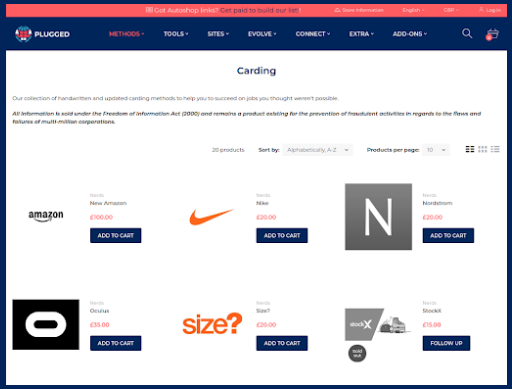
In order to justify the existence of the marketplace, Nerds claims to be operating “under the Freedom of Information Act (2000),” adding that Plugged takes advantage of “flaws and failures of multi-million corporations.”
How It Works
No invite link or referral is required to enter the Plugged marketplace or to create a new user on the site.
While many marketplaces demand an initial fee for viewing items or registering users, Plugged does not require any prepayment. New customers provide only their name and email address.
The delivery of most products is done by email, while any physical items are sent to the dropping addresses that are also available for purchase on the website. As is common in the underground community, the marketplace also offers multiple escrow options – ensuring both seller and buyer are accepting the deals that are made.
Shoppers on Plugged can buy items used for committing digital crimes, including various carding methods, manuals for stealing accounts and credit cards, and physical items used in such operations. The payment is done using cryptocurrencies or by means of Amazon gift cards in the UK.
Structure of the Plugged Website
The marketplace is divided into several sections. Every item includes a detailed description of what it contains and includes notes about the item – such as the countries in which it can be used. The prices range from tens to thousands of pounds. Lately, there have been discounts due to the Coronavirus situation.
The sections of the Plugged website include:
- Methods – Different kinds of carding methods divided into categories and countries. The categories represent different phases in the carding process such as loading and caching stolen goods. This is the core business of the marketplace.
- Tools – Physical devices, such as devices for SIM swapping and ID printing, as well as digital goods such as spoof scripts, phishing pages, SMS gateways for sending spam, and hosting providers.
- Sites – Platforms for building marketplaces and running illegal businesses.
- Evolve – Courses for self-development and mentoring in the hacking world. This section includes guides to performing multiple attacks and scams, and courses about how to conduct these activities securely. Courses consist of lectures by Nerds through ICQ, Wickr and Keybase. In addition, this section also lists VIP access to private communities, bots, dropping addresses, and opportunities to become a seller on Plugged. Customers can buy gift cards for Plugged and exchange coins using stolen credit cards.

Mentions of Plugged in Underground Communities
CyberProof’s CTI team conducted research into mentions of Plugged in underground communities using a variety of threat intelligence methods. The research revealed that some users have been searching for reviews about the marketplace – particularly, since there is not much mention of it in the more well-known underground communities. However, some users do mention Plugged on carding-related Telegram channels, and they report that use of Plugged has increased.
On other Telegram channels, several threat actors offered their carding services and noted that these services could also be purchased on Plugged. The users offered spamming and carding classes and American Express credit cards and phishing pages.
CyberProof CTI Team Assessment of Plugged
Our threat intelligence research indicates that Plugged is still in the nascent stage its business – trying to expand its market share by encouraging people to sell products on the website, and aiming to become one of the most prominent marketplaces in the cybercrime community.
Although it is relatively new, the prices of goods are quite high in some cases. This might be indicative of how useful the various methods and goods are.
Furthermore, we can see how important it is to build a good reputation within the cyber crime community by providing support services that assist with simple and friction free transactions.
Cyber crime is certainly nothing new – but since the outbreak of the COVID-19 pandemic, the prevalence of cyber crime is greater than ever. It’s essential to follow best practices for cyber security and leverage the benefits of tailored threat intelligence to keep your organization safe.
If you are concerned about the robustness of your organization’s cyber security operations and its ability to protect itself from cyber attacks or would like to speak with one of our experts, contact us today. We are here to help!
To learn more about best practices in protecting your organization from cyber threat, check out our Attack Use Cases.



