The first line of defense for any organization is at the physical perimeter of the building or campus, which may be protected by gates, locks, security guards, closed-circuit TVs, front desk personnel, and more. This is especially true when it comes to implementing a cyber security perimeter defense for areas like the server room where sensitive data - a high value resource - is stored.
But even using perimeter barriers and intrusion-detection devices, how effective are most organizations at protecting the perimeter? Despite the immense amount of money invested annually in perimeter defenses, and the startling size of the industry – $34.3Bn was the total value of world production of physical security products for 2019 – most organizations have glaring holes in basic protection at the physical perimeter.
It seems so simple – to keep the doors locked, for example, or to ensure security monitors are working effectively. Yet, perimeter defense is far from simple, and it’s crucial to cyber security to effectively protect your organization’s “crown jewels.” With so many of us working at home due to COVID-19 and offices only partially staffed, this may be more relevant than ever before.
Perimeter defense is far from simple, and its crucial to cyber security to effectively protect your organization's "crown jewels."
Let’s look at some of what needs to be done to improve an organization’s security at the perimeter.
Planning & Implementing a Secure System
The first step in securing the physical perimeter requires a careful check of an organization’s physical setup:
- Where is your organization’s perimeter? Establish exactly where the area you are protecting begins and ends. Is it a building? A limited area within a building? A campus? Or an outdoor area?
- Defining the risk – Who is considered a security risk? Is it “just” the employees, or does it include the cleaning staff? Outside consultants? Former staff members who no longer work for the organization? What about the building contractors and construction workers, who are intimately familiar with the building’s architecture and design?
- Office seating – Mixing departments in one room can lead to breaches of security. For example, an HR professional seated near employees from other departments may allow people outside of HR to access salary information, which should remain confidential.
- Mapping out sensitivity levels – Establishing that the server room has a high sensitivity level, for example, but that the kitchen or gym have low sensitivity levels. Rooms with high sensitivity levels should be behind locked doors.
- Paper disposal – How do you dispose of confidential documentation? Can employees print out any document? Is there a paper shredder? Shredding paper helps maintain customer privacy, reduces the risk of identity theft, and protects key information like plans or prototypes from being stolen. In the healthcare industry, destroying personal information is mandated by the Health Insurance Portability and Accountability Act (HIPAA).
- Limiting physical access – Do you lock the building at times when employees are not expected to be working? Should you consider limiting access for part-time employees (based on their schedules)? Can you track the presence of employees or visitors at unexpected times? And while it's great to have a security guard at the entrance to the building – do you also have one at the entrance to the parking lot? Do you register every person who comes in or out of the building?
- Raising employee awareness – Employees should be trained to be vigilant when allowing visitors into the organization and to report suspicious activity.
Physical Perimeter Security is Linked to Information Security
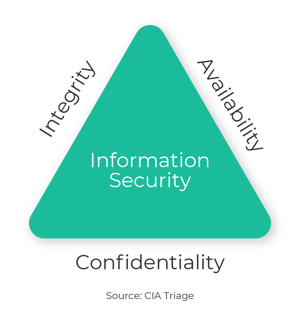
The American Central Intelligence Agency (CIA) refers to the CIA Triad – a model for the development of security policies that relies on three “legs”: Confidentiality, Integrity and Availability.
The CIA Triad reflects a fundamental truth: in today’s world, it is essential for organizations to protect sensitive data from unauthorized access.
As pointed out in Adnan Raj’s article on multi-factor authentication in The Atlantic, privacy regulations like General Data Protection Regulation (GDPR) place tremendous demand on any organization handling sensitive data – to ensure the data’s integrity and keep it secure.
And protecting your data starts with a perimeter defense that includes limiting physical access.
That means employees need to be authorized to enter certain areas or to access specific parts of the network. One obvious example, to illustrate the point: only a minimal number of employees should have permission to enter the server room in order to limit the possibility of someone doing damage – intended or malicious.
The techniques for limiting access to sensitive data include, but are not limited to:
- Employee ID cards or biometric fingerprint authentication
- Registration of visitors
- Escorting visitors in and out of work premises
- Doors that limit entrance to just one person at a time
- Security cameras
- Inspections at random times
- Periodic validation and update of employee authorization
- Questionnaires and reliability tests during the interview process
- Security guards at the entrance of the parking lot
- Alarm systems for documenting and monitoring unauthorized access
- Developing a prepared response in case of a security event, including escalation processes and internal & external reporting
Why Cyber Security Strategy Includes Pen Testing – The Nitty Gritty of Breaking In
Penetration tests are an important way to check the effectiveness of your organization’s security system at the physical perimeter.
But how do pen tests work? Let’s look at some of the more common strategies:

- Social engineering
- Leveraging weaknesses in the security system
The Dangers of Social Engineering
Information gained through social engineering can be used by anyone who wants to cause damage – for example, a current or former employee who wants to hurt the organization, people coming from competing organizations, or hackers interested in leveraging an attack for ransom. Here are some of the classic methods of attack that are used to break in:
- The security guard – Befriend the guard, and ask him or her to do you a favor and let you in. Or pretend to be the guard’s manager – and in this guise, phone the guard and ask him or her to let someone else in.
- Piggybacking – Find an employee who you can be in touch with directly and ask him or her to wait for you at the entrance and open the door for you.
- Forged ID – Find a way to duplicate an employee’s ID card – by standing near the employee outside the building and taking a picture of the card.
Leveraging Technical Weaknesses in the Security System
Another system involves identifying the vulnerability in the existing security system. For example:

- Slipping through the front door – Pushing yourself quickly through the door, when it’s opened by an employee
- Taking advantage of one-way sensors – Walking into the building when the doors open because someone has come out, that is, if the sensors are only one way
- Breaking in – Using classic techniques such as climbing over a fence that’s not high enough, breaking open a lock, or identifying unlocked doors
- Drones – You can use a drone to penetrate a campus and take photographs that help you figure out the weaknesses in an organization’s security system
Once the Perimeter Has Been Penetrated…
Physical penetration of a campus or building is frequently the first step in the attempt of malicious actors to gain access to an organization’s data.
Here are just a few of the many ways that criminals can cause damage, once they are inside the physical perimeter:
- Breaking into the server room and damaging the servers
- Shutting down the phone system
- Photographing confidential documents or “shoulder surfing” – i.e., eavesdropping on confidential conversations
- Identifying laptops left unattended that are not locked (when an employee gets up to use the bathroom, for example), and infecting the computer with malware using USBs
- Photographing or stealing confidential documents from the garbage bins or the paper shredder, or photographing information on an unlocked computer that an employee left unattended
- Looking for memo notes that have been left on the desks of employees, that list usernames and passwords
- Phoning an employee from an internal telephone line, pretending to be the IT department and asking the employee for his or her password
And the truth is that penetrating the perimeter does not necessarily require walking through the front door. If the CEO’s computer “happens” to be pointed in the direction of the window of a competing company, for example, that means there could be computers in the adjacent building that can record all of the CEO’s correspondence and steal his or her ideas.
Bottom Line: Plan, Monitor, Test, Learn – Repeat
Effective access control procedures combined with perimeter barriers and intrusion-detection devices are important to improving the effectiveness of any organization’s security. However, these aspects of security are not enough.
What’s necessary is a process of conducting pen tests and generating reports that show the weaknesses that were uncovered, then reviewing these reports and initiating an ongoing cycle of improvement – to ensure your organization’s data stays safe.
Check out our Threat Alerts to learn how you can stay one step ahead – making the most of security automation.


